Generate my own seeds and Azure CSV file for programmable tokens
 With Azure MFA OATH tokens functionality, you are expected to receive a CSV file from us and upload it to Azure portal (this feature requires Azure AD (Microsoft Entra ID) Premium license, P1 or P2). With classic tokens, this file contains the factory set seeds and the seeds cannot be modified.
With Azure MFA OATH tokens functionality, you are expected to receive a CSV file from us and upload it to Azure portal (this feature requires Azure AD (Microsoft Entra ID) Premium license, P1 or P2). With classic tokens, this file contains the factory set seeds and the seeds cannot be modified.
In this guide, we will instruct how this can be achieved using our TOTPToolset app.
- You can use both the online version of TOTPToolset or download and launch Token2 TOTP Toolset - local. You may want to run this app on a computer that is fully offline (or firewalled) to be sure no information is being transferred to third parties
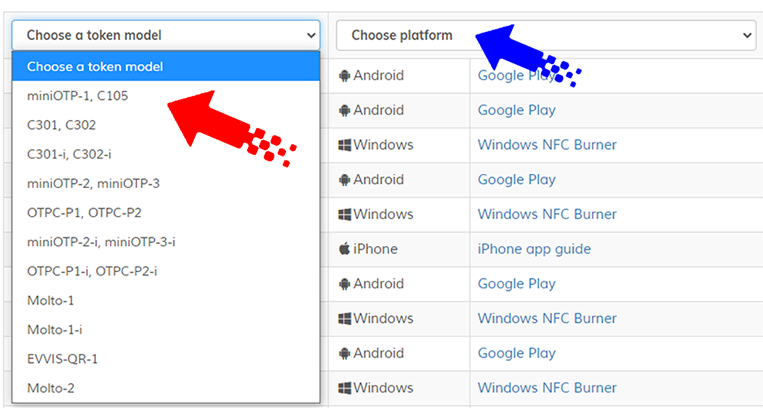
- Install one of the provisioning app to be used with your token. Please use this page to find the corresponding version.
Optionally, after the app has been installed, you can set the device to flight mode with Bluetooth, Wifi and Cellular data off to ensure no data will be transferred outside - Generate a random seed using Token2 TOTP Toolset. You can generate using the standard method or "true random" method, relying on online randomization service.
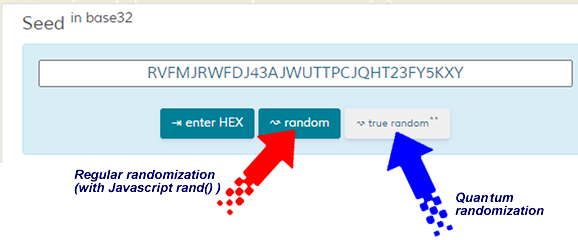
Important: Do not start the process without clicking on one of the randomization options. The default seed shown on the page is not randomized. - After the seed is generated, burn the seed using the provisioning app (NFC Burner or USB Config tool):
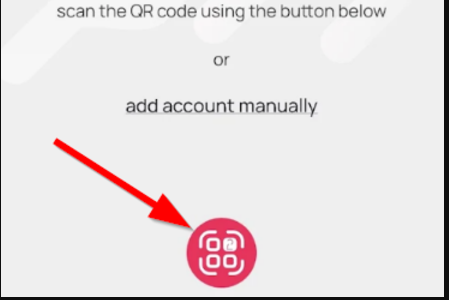
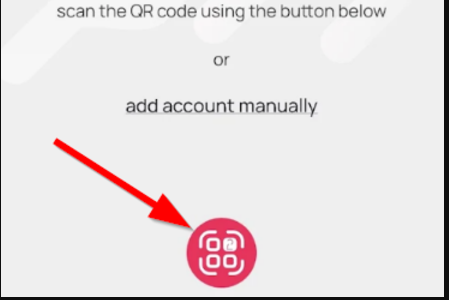
- Launch the NFC burner app on your Android device and hit the "QR" button
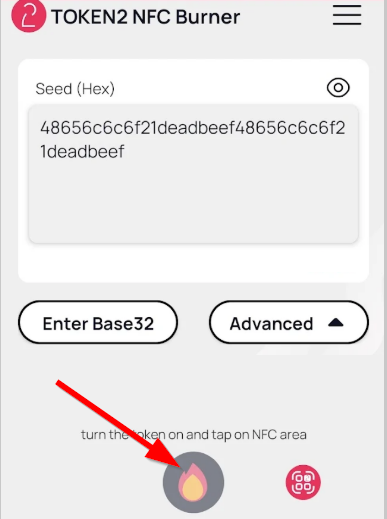
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear
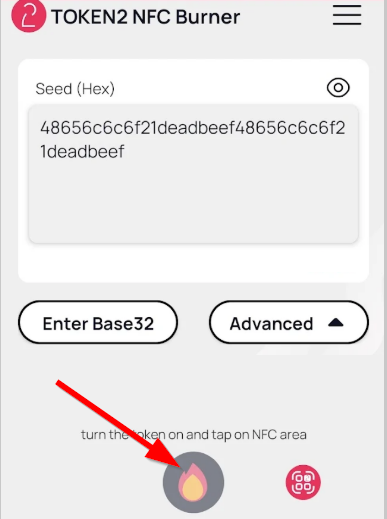
- Turn on the token and touch it with your phone (make sure it is overlapped by the NFC antenna) and click "Connect" on the app
- Upon successful connection, click the "Burn seed" button (the button will become active only if NFC link is established).
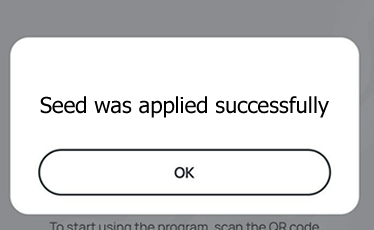
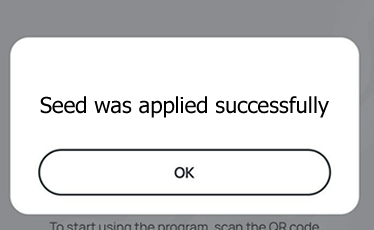
- A message box similar to the one below will be shown upon successful completion
Follow the steps below to perform setting the seed for your token using Windows App.
1. Launch the exe file, then select the NFC device from the drop-down list and click on "Connect". You should see a message box notifying about a successful operation.
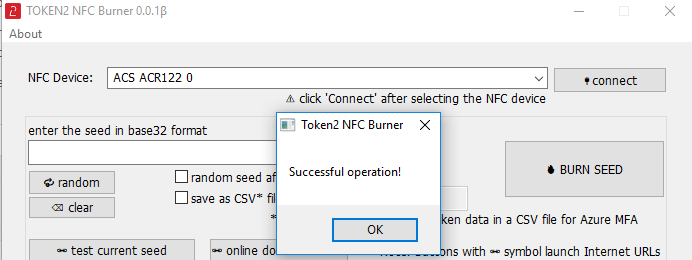
2. Enter or paste the seed in base32 format, or use one of the QR scanning methods to populate this field
3. Place the token onto the NFC module and wait for its serial number to appear.
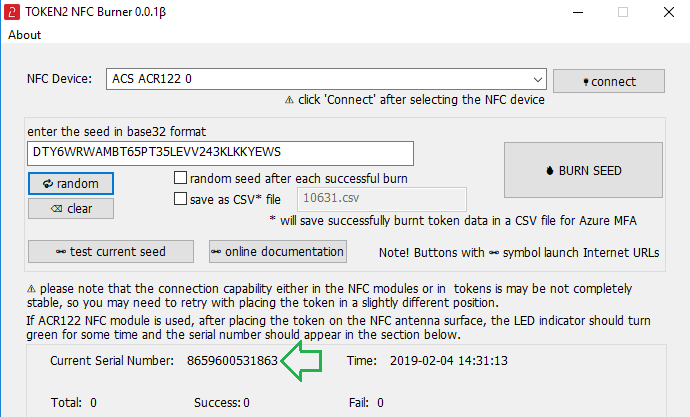
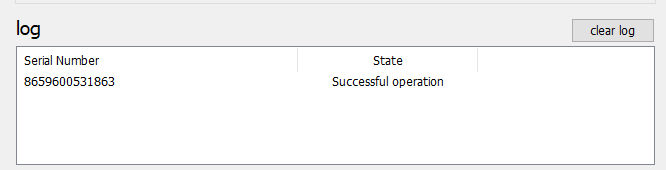
4. Click on "Burn seed" button. A log entry with the serial number and "Successful operation" text will be logged in the log window.
- Launch the NFC burner app on your iPhone device and hit the "scan QR" button
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear and the seed field will be populated with the hex value of the seed. Touch the Burn button to continue.
- When an NFC prompt similar to the one below is shown, turn on the token and touch the top of your iPhone with the token.
- A message box similar to the one below will be shown upon successful completion
Please note that the procedures above are shown only as examples and are valid to single profile TOTP tokens only. The procedure for multi-profile and USB-programmable devices are similar but slightly different - Launch the NFC burner app on your Android device and hit the "QR" button
- Verify the OTP shown on the device with the OTP value shown on the TOTP Toolset
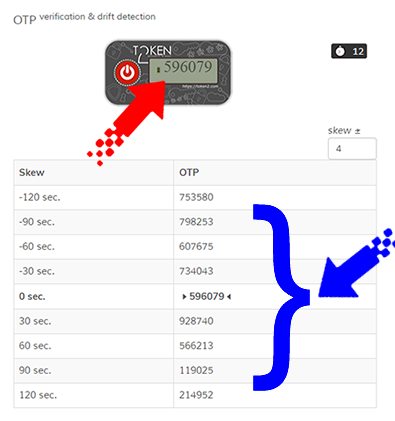
Important: If your OTP is not displayed on the virtual token, look in the table beneath. You can also try to increase the skew value (which is ± 4 by default). If the skew is more than 420 seconds, it is highly recommended adjusting the time on the token where possible, as the time drift tolerance in Azure MFA is 450 seconds. - Enter the serial number of your token and the username in UPN format to the relevant fields on the TOTP Toolset and click on " ⇲ append to CSV" button
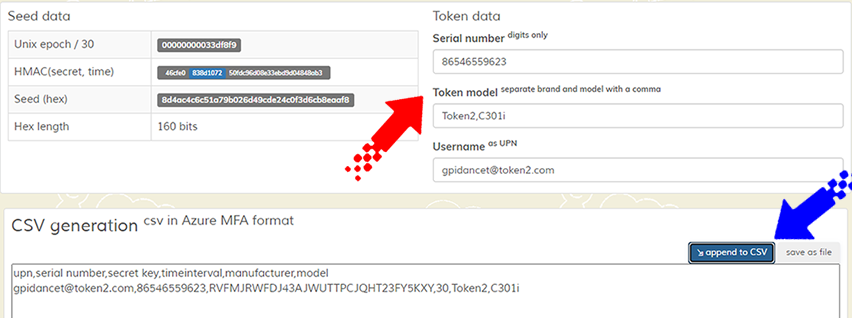
- Repeat steps 3 to 6 for every token you are provisioning
- Click on "save as file" button and save your MFA CSV file
- Import the CSV to Azure MFA as described in this guide
- Your tokens are ready to be activated for users
Command-line tools
Utilizing command-line tools can also streamline the process of automating seed generation. The following example demonstrates the utilization of the token2-config.exe tool, a Windows command-line utility designed for provisioning our second-generation NFC programmable TOTP tokens. An external NFC Writer device may be required for this method.Generate and burn random seeds using PowerShell
Open PowerShell session or create a ps1 script with the commands below:
1..32 | % { [String]$randkey += $(Get-Random -InputObject A,B,C,D,E,F,G,H,I,J,K,L,M,N,O,P,Q,R,S,T,U,V,W,X,Y,Z,2,3,4,5,6,7) }
# Execute the command with the generated seed
$cmd = "token2-config.exe --seed $randkey --results-file token2_result.txt"
Invoke-Expression $cmd
This will generate a random string of characters (letters A to Z and numbers 2 to 7, which is the base32 alphabet) and then use that string as a seed for a command-line executable (token2-config.exe) while also saving the results to a file (token2_result.txt). This file will contain the serial numbers of the tokens provisioned along with the written seed value, and can be used, for example, to create a csv file for Azure (Entra ID) MFA.
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!
