Virtual TOTP Tokens and converters
TOTP Toolset
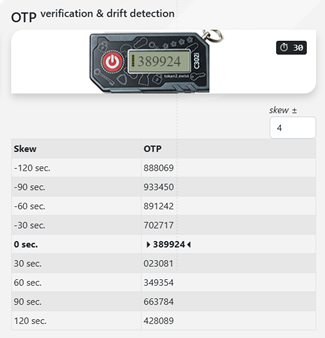
This open-source toolset provides a comprehensive set of utilities for working with time-based one-time passwords (TOTP). It can be used to emulate a hardware token, perform OTP verification, and detect time drift between tokens and authentication servers, making it a valuable resource for both testing and operational environments.
In addition, the toolset supports the generation of secure random seeds for programmable hardware tokens. These seeds can be exported in both CSV and JSON formats, specifically tailored for seamless integration with Microsoft Entra ID. This simplifies large-scale deployments and provisioning workflows.
The toolset is available in both SHA-1 and SHA-256 variants, allowing compatibility with a wide range of systems and security requirements, including modern environments that require stronger hashing algorithms.
For convenience, generated data can be recorded and exported for further processing, auditing, or direct import into identity platforms, as described here.
The source code of the Token2 TOTP Toolset is publicly available in our GitHub repository, enabling transparency, customization, and community contributions. If you prefer not to run it locally, you can also access the hosted version for immediate use..
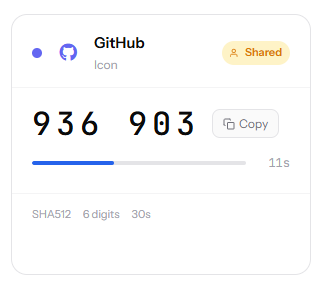
TOTPVault
A self-hosted TOTP manager built with PHP. Secret keys are AES-256-GCM encrypted on the server and never transmitted to the client. OTP codes are generated server-side and can be shared with teammates without ever exposing the underlying secrets.
Secure OTP management with server-side generation ensures secrets are decrypted only in memory and never exposed to the browser, while AES-256-GCM encryption protects data at rest using unique nonces. It supports flexible authentication via OAuth (Google, Microsoft, GitHub) or passwordless email links, and allows safe token sharing without revealing secrets. Users can import tokens via QR codes (including Google Authenticator bulk migration), customize them with icons and colours, and benefit from full RFC 6238 compatibility (multiple algorithms, code lengths, and intervals). A hide mode adds extra protection by briefly revealing codes before masking them again.
read more
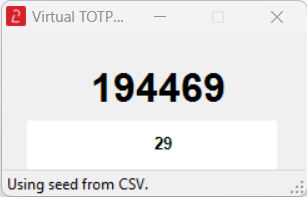
Virtual TOTP Token Tool for Windows
The Virtual TOTP Token Tool is designed to emulate Time-Based One-Time Passwords (TOTPs) for testing purposes. It enables users to generate TOTPs without the need to purchase physical tokens. This tool is particularly useful for customers testing procedures involving TOTP tokens with Azure Multi-Factor Authentication (MFA). It is a GUI app; you will see a window displaying the 6-digit OTP (refreshing every 30 seconds), fully emulating a hardware token.
t2otp.exe - command-line tool
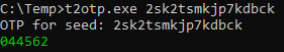 This tool is created as a command-line emulator of Token2 hardware tokens. It can generate any combination of 6 or 8 digits OTP, with 30 or 60 seconds interval, with SHA1 or SHA256 secret keys. Click here for more information and download.
This tool is created as a command-line emulator of Token2 hardware tokens. It can generate any combination of 6 or 8 digits OTP, with 30 or 60 seconds interval, with SHA1 or SHA256 secret keys. Click here for more information and download.
totp_generator.py - A Simple TOTP Code Generator with Skew Support
If you are a fan of Python (or prefer to view the source code of the tools you are using), here is the Python version of the same tool. This Python script allows you to generate Time-based One-Time Passwords (TOTP) using the PyOTP library. It also provides TOTP codes with a time skew, displaying multiple OTPs around the current time.
This is how the results will appear:
python totp_generator.py your_secret_key --num-otp 5 Time: 2023-10-11 15:10:30, TOTP code: 123456 Time: 2023-10-11 15:10:00, TOTP code: 789012 Time: 2023-10-11 15:09:30, TOTP code: 345678 Time: 2023-10-11 15:09:00, TOTP code: 901234 Time: 2023-10-11 15:08:30, TOTP code: 456789
Download totp_generator.py from GitHub
base32-to-hex-converter
A powershell script to convert files containing TOTP seeds(secrets) from base32 format to hex. The main use case is to convert Azure MFA CSV file to DUO-Compatible TOTP Import file
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!
