Buy options
€22.00| Model Number | OTPC-P2-i Nonbranded |
|---|---|
| Form-factor | credit card |
| Functions | TOTP configurable |
| Dimensions | 85.6×54×0.9 mm |
| Weight | 5 gr |
| Programmable |
1 profile restricted tyme sync |
| Product ID | T2-63 |
| Wordpress | fully compatible | |
|---|---|---|
| Google Account | fully compatible | |
| Azure On-Prem MFA Server | fully compatible | |
| Azure Cloud MFA / Office 365 AD Premium P1 or P2 | fully compatible | |
| Azure Cloud MFA / Office 365 AD Free/Basic | fully compatible | |
| Stripe Dashboard | fully compatible | |
| Meraki Dashboard | fully compatible | |
| ISDecisions UserLock | fully compatible | |
| ESET Secure Authentication | fully compatible | |
| Watchguard AuthPoint | fully compatible | |
This list is far from complete; we only highlight some featured supported systems. Listing all compatible systems would make the list very long. Check with us for more details: |
contact us |
|
If the system you are using is not included in the compatibility list, it does not necessarily indicate incompatibility. We encourage you to refer to our integration guides page or get in touch with us for more information. | ||
Please check product and platform compatibility before placing an order
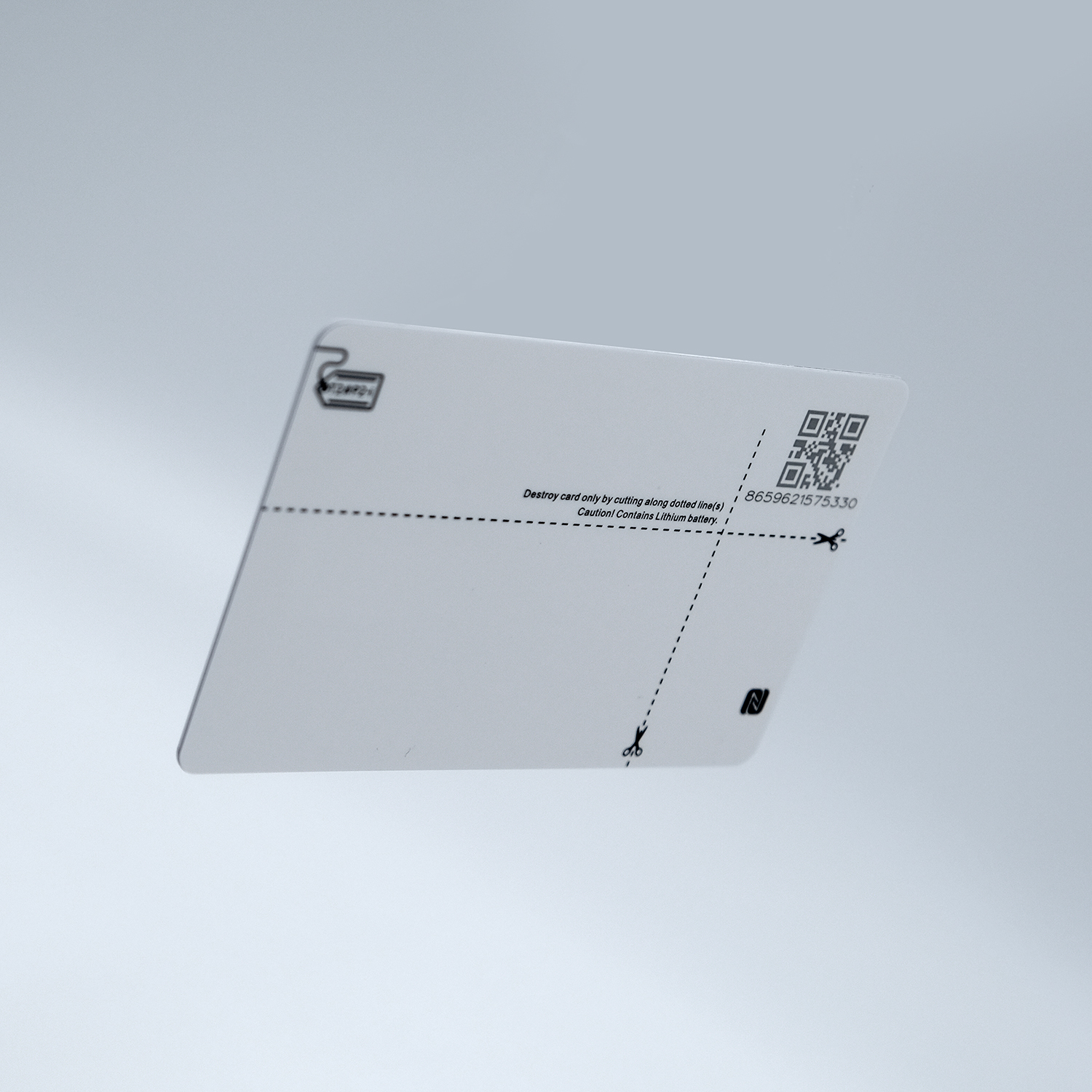
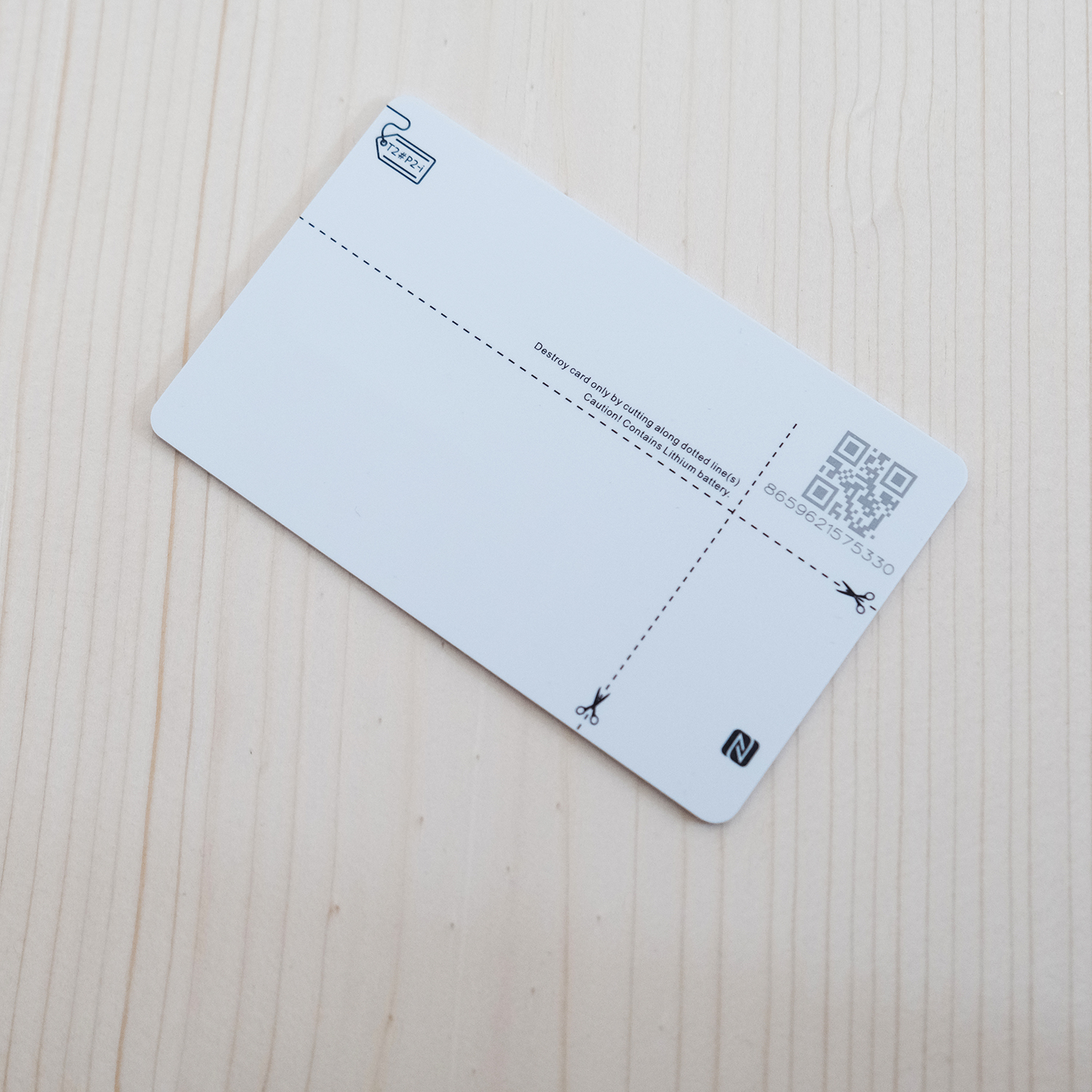
All pictures shown are for illustration purpose only. Actual product may slightly vary due to product enhancement or other reasons.
The seeds can be set and reset an unlimited number of times using Token2 NFC burner Android, iPhone and Windows applications.
Specifications
Form-factor: standard credit card - nonbranded
Algorithm: TOTP
Time offset: 30 seconds or 60 seconds [configurable]
Number of digits: 6
Hash algorithm: sha1 (default) or sha256 (set using NFC burner)
Screen type: e-Ink
Screen size: 24 × 7 mm
Dimensions: 85.60 × 53.98 × 0.9 mm
Weight: 5 gr
Expected lifetime: 4-5 years
Programmable: Yes
Time sync: Yes [restricted: setting time will clear the seed]
Maximal seed length : 63 bytes (126 hex / 101 base32)
Hash type: sha-1 or sha-256 [configurable]
Blog
21-12-2025
Android, NFC, and the Missing Piece of WebAuthn
 For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
19-12-2025
Streamline Token2 Classic Tokens in Okta
 Token2 classic hardware tokens provide phishing-resistant multi-factor authentication for your Okta environment. Our updated integration guide shows you how to deploy them using Okta's Custom OTP authenticator method.
Token2 classic hardware tokens provide phishing-resistant multi-factor authentication for your Okta environment. Our updated integration guide shows you how to deploy them using Okta's Custom OTP authenticator method.
09-12-2025
Framework ExpansionCard Enclosure for Token2 Keys
 Framework laptops are all about modularity. The Framework ExpansionCard 3D-printable enclosure for Token2 PIN+ Type-C keys brings FIDO2 security directly into your device.
Framework laptops are all about modularity. The Framework ExpansionCard 3D-printable enclosure for Token2 PIN+ Type-C keys brings FIDO2 security directly into your device.